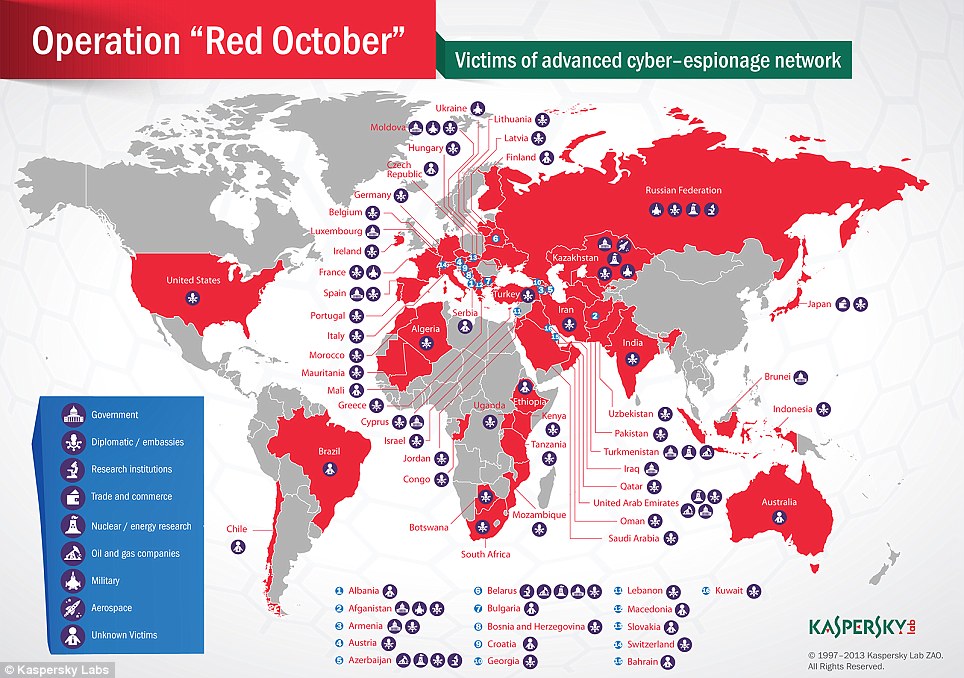
Kaspersky Lab has uncovered Operation Red October, (Rocra) a 5-year scheme by the Chinese and Russians to steal diplomatic, industrial and scientific data from Eastern Europe, North America and Asian organizations. Beginning in 2007, intelligence gathering operations were conducted in the form of attacks by cybercriminals toward Western nations. The thought is that this is in retribution on behalf of Iran for the damage caused to their country.
Encrypted files and decryption keys used by the European Union and NATO have been compromised. The countries under attack are:
• The Russian Federation
• Kazakhstan
• Azerbaijan
• Belgium
• India
• Afghanistan
• Armenia
• Ukraine
• Turkmenistan
Kaspersky said: “The information we have collected so far does not appear to point toward any specific location; however, two important factors stand out: The exploits appear to have been created by Chinese hackers, (and) the Rocra malware modules have been created by Russian-speaking operatives.”
Rocra appears to have been controlled by 60 command-and-control servers that were held in Germany and Russia. It is suspected that there is another “mother ship” server based in an unknown location.
Some of the attacks appear to be tailor-made for the victim with an estimated 1,000 different modules that performed specific attacks. Kaspersky explained: “For instance, the initial documents are customized to make them more appealing and every single module is specifically compiled for the victim with a unique victim ID inside (and) later, there is a high degree of interaction between the attackers and the victim. Compared to Flame and Gauss, which are highly automated cyber-espionage campaigns, Rocra is a lot more ‘personal’ and finely tuned for the victims.”
The software is broken down to continually run within the system until triggered to activate. Examples are stealing information from a connection made by a mobile phone or syphoning mail servers and downloading emails.
Although Kaspersky Lab admits that these attacks have not definitively been connected to China or Russia, it is assumed that the data collected would be yield a high price on the black market.
Kaspersky stated: “The information stolen by the attackers is obviously of the highest level and includes geopolitical data which can be used by nation states. Such information could be traded in the underground and sold to the highest bidder, which can be, of course, anywhere.”
Rocra is able to map out the internal layout of a network and information routes taken by computer software to take files with the use of thumb drives and smartphones.
In 2012, the US House Intelligence Committee (USHIC) warned American corporations in a new report against conducting business with 2 Chinese firms because of national security threats. Both Huawei Technologies and ZTE, two of the world’s largest telecommunications corporations and suppliers of cellular phones and technology are being highlighted by the US government and blamed for cyber-attacks. It is also claimed by the USHIC that they are involved in digital espionage.
According to the report, “China has the means, opportunity, and motive to use telecommunications companies for malicious purposes. . . . The investigation concludes that the risks associated with Huawei’s and ZTE’s provision of equipment to U.S. critical infrastructure could undermine core U.S. national-security interests.”
It is claimed that former industry insiders provided intelligence to the US concerning Huawei’s violations of US laws such as immigration, bribery, and corruption as well as an alleged “pattern and practice” using pirated software in its US satellites.
The report stated that the Chinese corporations were employing intelligence sources as well as private sector companies and other unnamed entities that could and assumedly did steal trade secrets, sensitive information and prehistory data while simultaneously shipped infected hardware and software to the US with the intent to cause disruptions in national security during wartime.
Around the same time as the release of the report, an anonymous White House official said there was an attempt to hack into the executive branch’s computer system through an unclassified network. No data were removed, proving that this was not an actual hack. The nameless official said that the experiment was a “spear-phishing”.
The supposition is that China is behind these attacks because of a phishing expedition against Gmail accounts wherein several senior US government officials and military personnel were affected.
According to the other mainstream media outlets, “hackers linked to China’s government broke into one of the U.S. government’s most sensitive computer networks, breaching a system used by the White House Military Office for nuclear commands, according to defense and intelligence officials familiar with the incident.”
The official questioned explained that a connection to Bejing in the case of the cyber attack “highlights a failure of the Obama administration to press China on its persistent cyber attacks.”
In January, analysts at the Council on Foreign Relations (CFR) have confirmed that hackers traced to China attacked their system. The “drive-by” hacking utilized a pirated computer. To compound the problem, the analysts said that the hackers removed their malware and traces of their presence from CFR computer systems.
Recognizing China as becoming a formidable replacement to the US as the world’s superpower, the CFR has outlined specific responses to this crisis of supremacy. Citing Chinese internet policy, their disdain for freedom of speech in social media, and influence in global cyberspace, the CFR appreciates that this rising “foe” must be confronted indirectly with propaganda to distract from the obvious.
This attack marked a new level of attack by international hackers who aim to steal information from government websites and computers. The “drive-by” tactic covertly plants malware, then the website itself is used to attack visitors to the site. Visitors can be infected as hackers will them attempt to hack into other computers as visitors are passing by. The hackers use the main site as a “watering hole” that attacks users to it for the hackers to steal information from their computers.